
24th April 2026 – I A S User Codes – Manufactures 2FA & Biometrics
Intruder Alarm Systems Manufacturers 2-Factor Authentication
Intruder Alarm Manufacturers & 2FA Support (2026)


Here’s the current landscape based on manufacturer statements and system capabilities:
Pyronix
❌ 2FA not available yet
“Maybe in the future.”
Texecom — Dual Code
✔️ Supports 2‑factor via Dual Code
A user can only access an area when a second user code (with the Dual Code attribute) is entered.
“Dual Code users will also activate the ‘1st and 2nd Code’ output type.”
Scantronic
❌ 2FA not available yet
“Maybe in the future.”
Honeywell
❌ 2FA not available yet
“Maybe in the future.”
Orisec — 2FA Enabled
✔️ Fully supports 2‑factor authentication
Uses Code + Proximity Tag.
“Both are required to operate the system.”
Risco
❌ 2FA not available yet
“Maybe in the future.”
Johnson Controls
❌ 2FA not available yet
“Maybe in the future.” Although Qolsys control panel does take a picture if you arm or disarm
Biometrics
“Only You Can Be You” Biometrics Video
https://vimeo.com/862308998?fl=pl&fe=sh
To watch CTL & CLICK à youtube.com.
Summary of the IDEMIA “Only You Can Be You” Biometrics Video
The above video introduces Vincent, an IDEMIA expert who has spent his career designing and deploying biometric technologies. His focus is on building systems that deliver:
- High‑performance biometric identification and authentication
- Non‑biased, fair algorithms that work reliably across diverse populations
- Secure identity verification across both physical and digital environments
The central message is that identity is at the core of IDEMIA’s work, and their researchers are committed to ensuring biometric systems are accurate, ethical, and trustworthy.
- Emphasis on responsible, unbiased biometrics
- Ensuring security and performance at scale
- Applying biometrics to real‑world identity challenges
- Reinforcing the principle: “Only You Can Be You”
Identity should travel with the user, not live in a database. Just as IDEMIA’s biometric card performs fingerprint matching inside a 0.8 mm card, our next‑generation access credentials will authenticate users directly on the device — whether that’s a batteryless biometric token, a secure NFC credential, or a hybrid card‑plus‑mobile identity. This eliminates the weakest link in most access systems: centralised biometric storage.
Contactless must be both secure and hygienic.
The post‑COVID world accelerated demand for frictionless access. IDEMIA’s biometric terminals show how facial and fingerprint recognition can deliver secure, hygienic identity verification at scale. Elite Security Systems will extend this approach to doors, gates, cabinets, and restricted zones — enabling fast, touch‑free authentication without compromising auditability or compliance.
Biometric authentication works by capturing unique biological traits (like fingerprints, facial features, or voice patterns), storing them securely, and comparing them against live samples during login to verify identity.
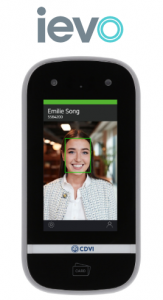
S-Key – Biometric access control card
In 2018, following the spinout of Sensyne, the Company focused on the application of its RF energy harvesting technology in the field of biometric smart cards, a rapidly developing field at the time. In 2022 the Company launched S-Key, a new batteryless biometric smart card that it had developed for access control applications.

S-Key is available in Mifare Classic or DESFire variants and will work out-the-box.
Key benefits & features when integrated with no additional infrastructure costs as it works out of the box with existing supported NFC MIFARE® Classic EV1 (all sizes) & · MIFARE® DESFire EV1/2/3 (all sizes) readers
All biometric data is stored on the card making GDPR and privacy compliance much simpler
S-KEY access cards are a battery-less solution which removes the cost of maintenance and helps deliver strong sustainability credentials
Hygienic contactless technology ideally suited to the post-COVID-19 world
Facial Recognition
Facial Recognition: High‑Throughput Identity Verification
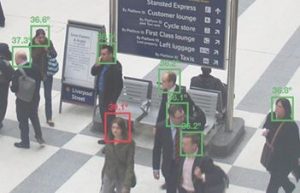
- Smooth, automated passage through airports & stadiums
- Real‑time identification of banned or unauthorised individuals
- Border‑control identity matching
- Deployed globally: US, UAE, Albania, India
- Supports crowd scanning & reserved‑area access
- Part of IDEMIA’s full biometric suite (fingerprint, iris, vein, e‑gates)
Facial recognition is now a critical component of high‑volume, high‑security environments.
Compliance: Data Protection & Surveillance Systems
“How can we comply with the data protection principles when using surveillance systems?”
And notes that guidance is being updated due to the Data (Use and Access) Act (19 June 2025).
This means organisations must prepare for:
- Updated retention rules
- Stricter transparency requirements
- Stronger justification for surveillance
- Enhanced biometric governance
Checklist
- Know why you’re using it – You must have a clear reason for installing cameras or sensors
- Be Fair and Open – Put up signs so people know they’re being recorded. Tell them who to contact if they have questions.
- Don’t Record More Than You Need – Point cameras only at the areas you need to protect. Avoid recording neighbours or private spaces. Turn off audio unless necessary.
- Keep Footage Safe – Only trusted people should have access. Use strong passwords. Keep footage only for as long as you need it
- Don’t Keep Footage for Too Long – Delete old recordings regularly. Keep footage for as long as you need it.
- Respect Peoples Rights – If someone ask to see footage of themselves you must respond. You may need to blur other people in the video
- Review the System Regularly – Make sure its still needed. Check that everything is working properly. Update your signs and documents if anything changes.
Conclusion
2FA and biometrics are no longer emerging technologies — they’re becoming core security expectations.
From Texecom’s Dual Code to Orisec’s 2FA, from IDEMIA’s ethical biometrics to the batteryless S‑Key, the industry is clearly moving toward:
- Decentralised identity
- Hygienic, contactless access
- Privacy‑first authentication
- Frictionless user experience
Thanks for reading
Marketing Department







